BGP Firewall
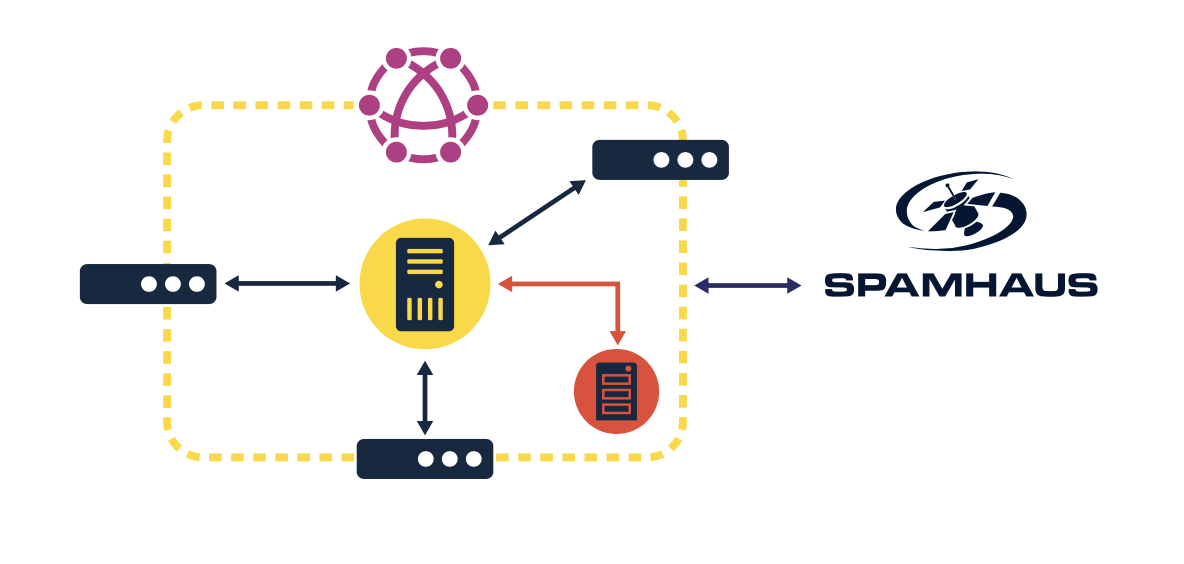
Use Spamhaus' highly-effective and accurate IP reputation data with your existing router or firewall.
Implementing threat intelligence at the router or firewall level can protect your system from connecting with the worst known, malicious IP addresses.
These feeds can be easily added to your organization’s existing routers DENY tables to stop communication with any IP addresses listed. Only the most malicious IP addresses are included in Spamhaus extremely BGP Feeds. Spamhaus BGP data feeds are expertly researched to have zero false positives. Extreme accuracy means the only the worst of the worst IP addresses will be blocked, without any concern of blocking legitimate traffic.
Adding BGP Feeds to your routing DENY table can protect against cyber threats at your network edge.
BGP Firewall Feeds include:
- DROP: Do Not Route or Peer
- eDROP: Extended Do Not Route or Peer
- Botnet Controller List (BCL) – Dedicated
- *New* Botnet Controller List (BCL) – Compromised
Prevent communication with malicious IPs, known to be involved in criminal activity, ransomware, malware, DDoS attacks and more.
Key Features & Benefits
Zero False Positives: Data feeds including in Spamhaus’ BGP Firewall are extremely accurate and designed only to block known malicious IP addresses.
Enhanced Protection: Prevent you users from connecting with known malicious IP addresses, including known botnets.
Expertly Researched Data: Spamhaus has 23+ years of experience researching threat intelligence. Over 13.4 Billion global SMTP connections, 1.5 million IPs, 3 million domains analyzed daily.
“Set and Forget” Product: No maintenance required after initial set up.
Affordable Option: Low cost solution that works with current router or firewall. No additional hardware is needed.
Quick Deployment: Users can add to existing infrastructure in minutes. Easily download to router’s DENY tables for instant protection.
BGP Firewall Data Feeds
Spamhaus offers the following data feeds, which can be configured into your existing router or firewall.
“Worst of the Worst” known networks under the control of cyber criminals. No legitimate traffic should be connecting with IP addresses contained on the DROP list.
DROP identifies networks that are used for:
- Malware hosting
- Botnet Command and Control host servers
- Networks involved in DDos attacks
Extended version of the DROP list (see above) containing net blocks sub-allocated under the control of cybercriminals.
Dedicated Botnet Controller List (BCL Ded) contains IP addresses that are:
- Botnet C&C infrastructure on dedicated host
- Used exclusively for Botnet control
Compromised Botnet Controller List contains single IPv4 addresses that are:
- Hosting Botnet Command & Control Servers
- Used to control bots (infected devices)
Start your free trial.
Design the best set of data feeds to meet your needs!
Experience improved cybersecurity and stop phishing emails, ransomware, malware, and other cyber threats. Sign up for your free consultation and receive an in-depth technical deep dive and a 30-day free trial.